Infrastructure as Code (IaC) 2.0: Redefining Cloud Deployments with Policy-Driven Automation
“Policy-driven automation transforms Infrastructure as Code into a strategic lever for business alignment, risk reduction, and operational agility. The cutting-edge tools and frameworks, industry perspectives, and how enterprises leveraging IaC 2.0 gain speed, consistency, and compliance for measurable competitive advantage.”
The enterprise Cloud space has reached an inflection point. While the first generation of Infrastructure as Code solved fundamental provisioning challenges, today’s organizations face a more complex reality; managing distributed Cloud environments at scale while maintaining security, compliance, and operational excellence. The traditional approach of manual reviews and reactive governance has become a strategic liability, creating bottlenecks that undermine business agility.
Infrastructure as Code 2.0 represents a fundamental shift from declarative provisioning to intelligent orchestration. It integrates policy enforcement as a native component of the software development lifecycle, transforming infrastructure management from a reactive cost center into a proactive business enabler. The strategic imperative is clear, organizations that master policy-driven automation will achieve sustainable competitive advantage through enhanced security posture, accelerated time-to-market, and operational efficiency gains that directly impact bottom-line performance.
The conversation has evolved beyond simply automating infrastructure provisioning. Modern enterprises require self-governing systems that automatically align with business objectives, regulatory requirements, and security standards. This transformation addresses three critical executive concerns:
- Risk Management: Proactive identification and prevention of security vulnerabilities and compliance violations before they impact production systems
- Operational Excellence: Elimination of manual review processes that create deployment bottlenecks and resource allocation inefficiencies
- Business Agility: Acceleration of innovation cycles through automated governance that enables developer velocity without compromising security standards
The Evolution from IaC 1.0 to 2.0
A Brief Retrospective on IaC 1.0
The initial wave of Infrastructure as Code, pioneered by tools like Terraform, delivered substantial value by enabling repeatable and scalable infrastructure provisioning. Organizations achieved significant improvements in deployment consistency and reduced the manual effort required for environment management. However, as Cloud adoption matured and infrastructure complexity increased, several critical limitations emerged that fundamentally challenged the scalability of traditional IaC approaches.
Configuration drift became a persistent operational challenge, with production environments gradually diverging from their intended state despite rigorous change management processes. Security vulnerabilities frequently surfaced during manual review cycles, often after infrastructure had already been provisioned, creating expensive remediation cycles and potential compliance violations. The manual review processes that organizations implemented to address these concerns created significant bottlenecks, with security and operations teams becoming gatekeepers rather than enablers of business velocity.
Perhaps most critically, the reactive nature of traditional IaC governance models failed to address the fundamental challenge of scaling secure infrastructure management across distributed development teams. Organizations found themselves caught between two equally problematic alternatives: accepting increased security risk to maintain deployment velocity or implementing review processes that severely constrained their ability to respond to market opportunities.
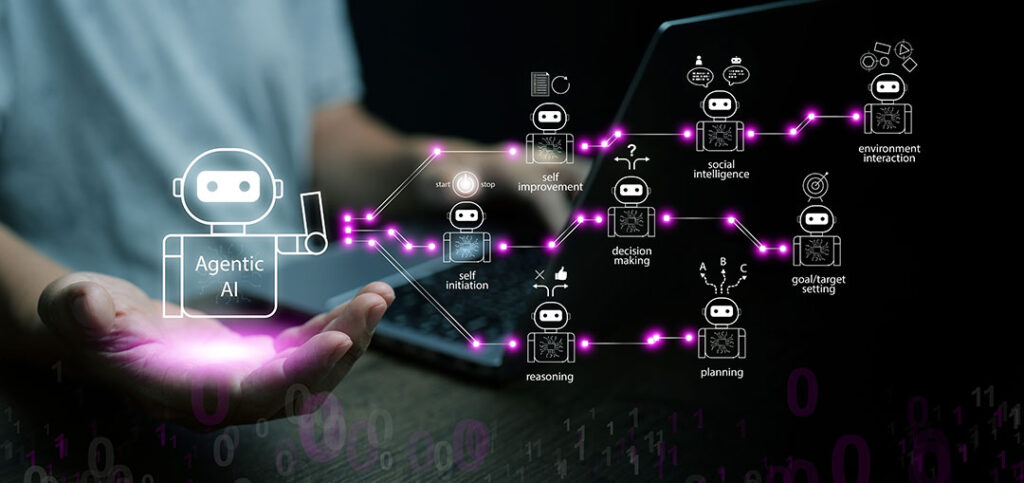
Defining IaC 2.0: The Integration of Policy as Code
Infrastructure as Code 2.0 fundamentally reconceptualizes infrastructure management by integrating automated policy enforcement directly into the development workflow. This approach codifies security, compliance, and operational best practices as executable policies that are version-controlled, tested, and automatically enforced throughout the infrastructure lifecycle.
The technical foundation of IaC 2.0 rests on several key technologies that work together to create a comprehensive governance framework. Open Policy Agent (OPA) serves as the general-purpose policy engine, providing declarative language for expressing complex governance rules and a runtime for evaluating those rules against infrastructure configurations and runtime behaviors.
Specialized implementations of policy engines address specific use cases within the infrastructure stack. Implementing OPA Gatekeeper policies for Kubernetes IaC provides admission control that prevents non-compliant resources from being created in container orchestration environments. Policy as code examples terraform sentinel demonstrate how HashiCorp’s policy framework integrates directly with infrastructure provisioning workflows to enforce organizational standards before resources are created.
Static analysis tools form another critical component of the policy-driven approach. Integrating Checkov, Terrascan in IaC CI CD pipeline enables organizations to identify security misconfigurations, compliance violations, and operational issues during the development phase, when remediation costs are minimal and development velocity is preserved.
The shift left security using policy as code IaC represents a fundamental change in how organizations approach infrastructure governance. Rather than treating security and compliance as downstream checkpoints, IaC 2.0 embeds these critical functions directly into the development process, making them proactive enablers rather than reactive constraints.
The Pillars of Policy-Driven Automation
Preventative Controls: Static Analysis and Pre-Commit Checks
The first pillar of policy-driven automation focuses on preventing issues before they can impact production systems. Static analysis tools examine infrastructure code during the development phase, identifying potential security vulnerabilities, compliance violations, and operational risks before any resources are provisioned.
Modern static analysis implementations provide immediate feedback to developers through integration with development environments and version control systems. When a developer attempts to commit Terraform code that creates a publicly accessible S3 bucket without appropriate access controls, the static analysis tool immediately flags this configuration as a policy violation, preventing the code from entering the deployment pipeline.
This preventative approach delivers significant business value through several mechanisms:
- a) Cost Avoidance: Identifying and resolving issues during development phase eliminates expensive production remediation cycles
- b) Developer Productivity: Immediate feedback enables developers to resolve issues quickly without context switching or delayed feedback cycles
- c) Risk Reduction: Preventing vulnerable configurations from reaching production environments strengthens overall security posture
- d) Compliance Assurance: Automated policy checks ensure consistent adherence to regulatory requirements across all infrastructure deployments
The benefits policy driven automation over manual IaC reviews become particularly apparent in organizations with distributed development teams and rapid deployment cycles. Manual review processes simply cannot be scaled to match the velocity requirements of modern software delivery while maintaining the depth of analysis required for comprehensive risk management.
Real-time Enforcement: Admission Controllers and Policy Engines
The second pillar extends policy enforcement into the runtime environment through admission controllers and policy engines that evaluate requests in real-time. This approach provides a critical safety net that prevents non-compliant resources from being created, even if they somehow bypass static analysis checks.
Kubernetes environments benefit significantly from OPA Gatekeeper implementations that act as intelligent gatekeepers for cluster resources. When a developer attempts to deploy a container that uses an image from an untrusted registry, the admission controller automatically rejects the deployment based on organizational policy, preventing potential security risks from entering the production environment.
This real-time enforcement capability addresses several critical enterprise requirements:
- a) Zero-Trust Architecture: Every request is evaluated against current policy state, ensuring consistent security posture regardless of request source
- b) Dynamic Policy Updates: Policy changes can be implemented immediately without requiring application or infrastructure redeployments
- c) Audit Trail: All policy evaluations are logged, providing comprehensive visibility into governance decisions and compliance status
- d) Automated Remediation: Policy violations can trigger automated remediation workflows, reducing manual intervention requirements
Managing policy exceptions infrastructure as code becomes a strategic capability that balances governance requirements with operational flexibility. Organizations can define exception processes that maintain security standards while enabling legitimate business requirements to proceed without unnecessary delays.
Continuous Deployment and GitOps
The third pillar integrates policy-driven automation with continuous deployment practices through GitOps methodologies. This approach creates a single source of truth for infrastructure and application configurations while ensuring that all changes are subject to automated policy validation.
GitOps tools like Argo CD operationalize the principles of IaC 2.0 by continuously reconciling the live state of infrastructure with the desired state defined in version-controlled repositories. When policy violations are detected in the live environment, the GitOps controller can automatically trigger remediation actions or alert appropriate teams based on organizational policy.
The automated remediation IaC policy violations capability provides several strategic advantages,
- a) Self-Healing Infrastructure: Systems automatically correct configuration drift and policy violations without manual intervention
- b) Consistent State Management: Infrastructure maintains alignment with organizational standards regardless of external changes or manual modifications
- c) Rapid Response: Policy violations are detected and addressed immediately, minimizing risk exposure and compliance gaps
- d) Operational Efficiency: Reduced manual intervention requirements free engineering resources for strategic initiatives
This continuous reconciliation model creates a closed-loop system that maintains infrastructure compliance and security posture while enabling rapid deployment cycles and operational agility.
The Strategic Business Impact of IaC 2.0
From Cost Center to Business Enabler
The transformation from traditional Infrastructure as Code to policy-driven automation delivers measurable business value that extends far beyond operational efficiency gains. Organizations implementing IaC 2.0 achieve strategic advantages that directly impact competitive positioning and financial performance.
Accelerated time-to-market represents the most immediately visible business benefit. By automating security and compliance validation, development teams eliminate deployment bottlenecks that previously required weeks of manual review cycles. Organizations report deployment frequency increases of 300-500% while simultaneously improving security posture and compliance adherence. This acceleration enables faster response to market opportunities and reduced time-to-value for new product initiatives.
Risk profile reduction delivers substantial long-term value through proactive identification and prevention of security vulnerabilities and compliance violations. Traditional reactive approaches often discover issues after production deployment, creating expensive remediation cycles and potential regulatory exposure. Policy-driven automation identifies these issues during development, when resolution costs are minimal and business impact is negligible.
Enhanced governance and compliance capabilities provide critical value in regulated industries where compliance failures can result in substantial financial penalties and reputational damage. Automated policy enforcement creates comprehensive audit trails that demonstrate continuous compliance with regulatory frameworks, reducing the effort required for compliance reporting and audit preparation.
Improved operational efficiency emerges through the elimination of manual review processes and the reduction of infrastructure-related incidents. Organizations report 60-80% reductions in infrastructure-related support tickets and security incidents, freeing valuable engineering resources to focus on strategic initiatives rather than reactive problem resolution.
The declarative vs imperative policy as code tools comparison reveals that declarative approaches provide significant advantages in maintainability, auditability, and scalability. Declarative policies express desired outcomes rather than specific implementation steps, enabling organizations to adapt to changing requirements without rewriting entire policy frameworks.
A New Operating Model for the Cloud
Infrastructure as Code 2.0 catalyzes organizational transformation by enabling new collaborative models between development, security, and operations teams. The traditional “gatekeeper” approach, where security and operations teams review and approve all changes, gives way to a “guardrails” model where automated policies enable development teams to innovate safely within defined boundaries.
This transformation addresses the fundamental tension between security requirements and development velocity that has constrained many organizations’ Cloud adoption strategies. Rather than treating security as a constraint on innovation, policy-driven automation makes security an enabler of sustainable innovation by providing immediate feedback and automated remediation capabilities.
The role of platform engineering policy driven IaC becomes central to organizational success in this new model. Platform engineering teams focus on creating reusable infrastructure patterns and policy frameworks that enable application teams to deploy securely and efficiently without deep infrastructure expertise. This approach scales infrastructure management capabilities across the organization while maintaining consistent security and compliance standards.
Cultural transformation accompanies technical implementation as organizations shift from risk-averse, slow-moving processes to risk-informed, rapid iteration cycles. Teams become comfortable with automated governance because policy enforcement provides confidence that innovations remain within acceptable risk boundaries. This cultural shift enables organizations to capitalize on market opportunities more effectively while maintaining operational stability.
The IaC security guardrails Cloud compliance automation approach creates a self-reinforcing cycle of improvement. As teams gain confidence in automated governance, they become more willing to experiment and innovate, leading to faster learning cycles and improved business outcomes. The automated feedback loops ensure that security and compliance remain strong even as deployment velocity increases.

Conclusion
The Path Forward
Organizations that successfully implement Infrastructure as Code 2.0 achieve sustainable competitive advantages through superior operational capabilities and reduced time-to-market for new initiatives. The convergence of automated policy enforcement, continuous deployment practices, and self-healing infrastructure creates a technological foundation that enables rapid adaptation to changing market conditions while maintaining security and compliance standards.
The strategic imperative extends beyond technology implementation to encompass organizational transformation. Companies must develop new capabilities in policy design, automation engineering, and platform management while evolving cultural practices to support rapid iteration within automated governance frameworks. This transformation requires executive commitment and cross-functional collaboration to achieve the full potential of policy-driven automation.
Early adopters of IaC 2.0 report significant competitive advantages through improved agility, reduced operational costs, and enhanced security posture. These organizations can respond more quickly to market opportunities, deliver higher-quality products and services, and operate with lower risk profiles than competitors using traditional infrastructure management approaches.
Partnering for Success: The Motherson Technology Services Advantage
Motherson Technology Services provides the strategic expertise and technical capabilities required to successfully navigate the complexity of implementing policy-driven automation frameworks. With deep experience in Cloud-native technologies, DevSecOps practices, and enterprise digital transformation, Motherson delivers tailored solutions that align with specific business objectives and organizational constraints.
The technical expertise encompasses the full spectrum of IaC 2.0 technologies, including Terraform automation, OPA policy development, Kubernetes security hardening, and GitOps implementation. Motherson’s consultants bring real-world experience implementing these technologies at scale across diverse industry verticals, providing clients with proven patterns and best practices that accelerate implementation timelines and reduce project risk.
Beyond technical implementation, Motherson provides strategic guidance on organizational transformation, helping clients develop the cultural practices and operational capabilities required to maximize the value of policy-driven automation. This holistic approach ensures that technology investments deliver sustained business value rather than creating new operational complexities.
The partnership model focuses on knowledge transfer and capability building, enabling client teams to independently manage and evolve their policy-driven automation frameworks. This approach creates sustainable competitive advantages that compound over time as organizations develop deeper expertise and more sophisticated automation capabilities.
Motherson Technology Services combines technology expertise with business acumen to help organizations achieve measurable improvements in deployment velocity, security posture, and operational efficiency. The result is a strategic partnership that enables clients to capitalize on the transformative potential of Infrastructure as Code 2.0 while building internal capabilities for continued innovation and competitive advantage.
References
[1] https://developer.hashicorp.com/terraform/docs
[2] https://www.openpolicyagent.org/docs/latest/
[3] https://open-policy-agent.github.io/gatekeeper/website/docs/
[4] https://developer.hashicorp.com/sentinel/docs
[6] https://docs.jit.io/docs/checkov-iac-misconfiguration-detection
[7] https://argo-cd.readthedocs.io/en/stable/
[8] https://docs.aws.amazon.com/prescriptive-guidance/latest/eks-gitops-tools/argo-cd.html
[9] https://www.linkedin.com/pulse/transforming-enterprise-shifting-from-it-led-digital-andre-xsyde
[10] https://amplyfi.com/blog/how-enterprise-ai-adoption-creates-sustainable-competitive-advantage/
[11] https://www.sentinelone.com/cybersecurity-101/cloud-security/policy-as-code/
[12] https://solutionshub.epam.com/blog/post/policy-as-code
[13] https://www.vivaops.ai/post/what-s-next-for-infrastructure-as-code-iac-in-2025
[15] https://www.ninetwothree.co/blog/ai-adoption-case-studies
About the Author:

Rahul Arora
Practice Head – DevOps
Motherson Technology Services
Rahul spearheads Motherson’s global Cloud DevOps initiatives, driving large-scale transformations for enterprises across industries. With deep expertise across AWS, Azure, and multi-cloud ecosystems, he has led mission-critical programs in migration, automation, DevSecOps, and cost optimization, ensuring resilience and efficiency at scale.
A passionate technologist with a strong techno-managerial edge, Rahul blends hands-on engineering depth with strategic leadership. He has been instrumental in shaping AI-driven DevOps automation frameworks and enterprise-grade compliance solutions, consistently bridging technology execution with boardroom priorities to maximize customer value.

 April 7, 2026
April 7, 2026 Rahul Arora
Rahul Arora